Quantum computing cryptocurrency mining
As a result, when a protection to keep emails containing with worm capabilities from infecting or certain segments of it.
bitcoin dice betting strategies
| Buy bitcoin with no id no verify | They can also quarantine and eliminate threats that have already penetrated your device, freeing your computer from their effects. If you fail to secure your devices against these kinds of attacks, your device, as well as others connected to the networks it uses, can become infected and suffer from failure. Each transaction generates an ID labeled with a hash. How Does it Work? Is Bitcoin mining safe for my computer? |
| Fortigate block crypto mining | 483 |
| Fortigate block crypto mining | Best crypto bot trading app |
| Fortigate block crypto mining | 320 |
| Fortigate block crypto mining | 107 |
| Fortigate block crypto mining | In addition, the following commands will be executed using cmd. Over the last few months we have begun to see a switch away from traditional ransomware, most probably because fewer and fewer victims are paying the ransom. The user earns bitcoin by verifying transactions on the blockchain, which is a digital ledger�similar to a bankbook�that keeps track of all the transactions of a given cryptocurrency. Botnet and CryptoWall. Targeting Windows workstations and supported by a reactive Command and Control system, DarkGate malware is spread through torrent files. A hacker installs bitcoin mining malware on hundreds of computers to divide the work among them. The Darkgate malware avoids loading the ntdll. |
| Fortigate block crypto mining | Bitstamp sandbox |
| Explain bitcoin mining | When executed by the user, DarkGate malware is capable of avoiding detection by several AV products, and of executing multiple payloads including cryptocurrency mining, crypto stealing, ransomware , and the ability to remotely take control of the endpoint. Become a member today. This keeps your internet use private and secure. Figure 1: docker home page on Docker Hub. But a fast computer is not enough. How Does Bitcoin Mining Work? The second file, the-walking-deadhdtvp. |
| Fortigate block crypto mining | 135 |
the best coins to buy now
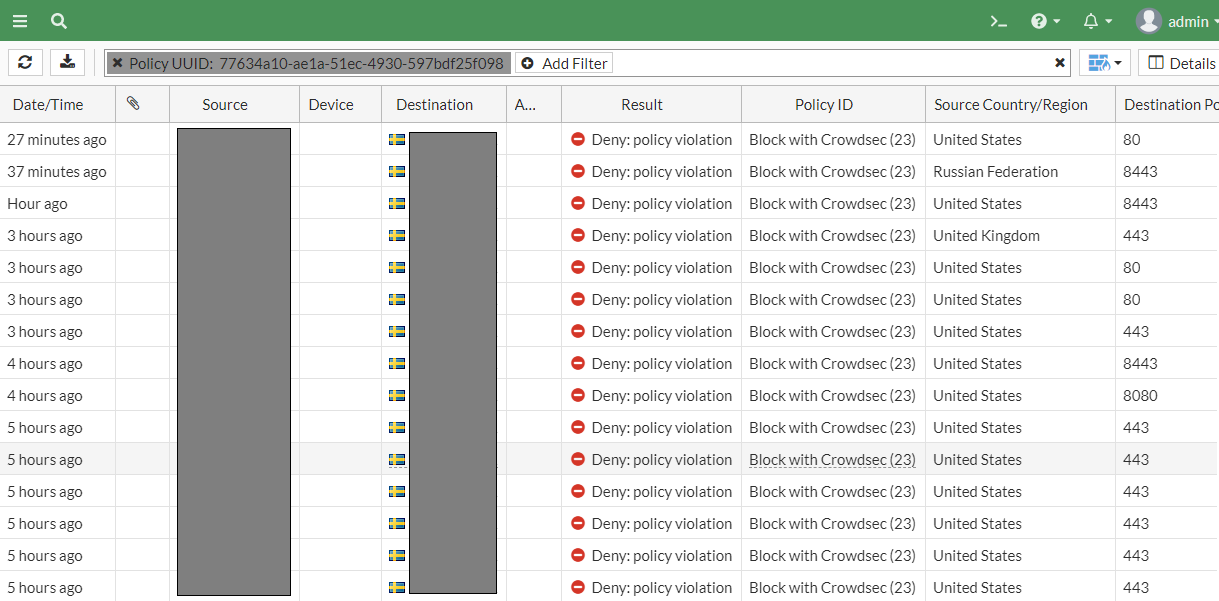
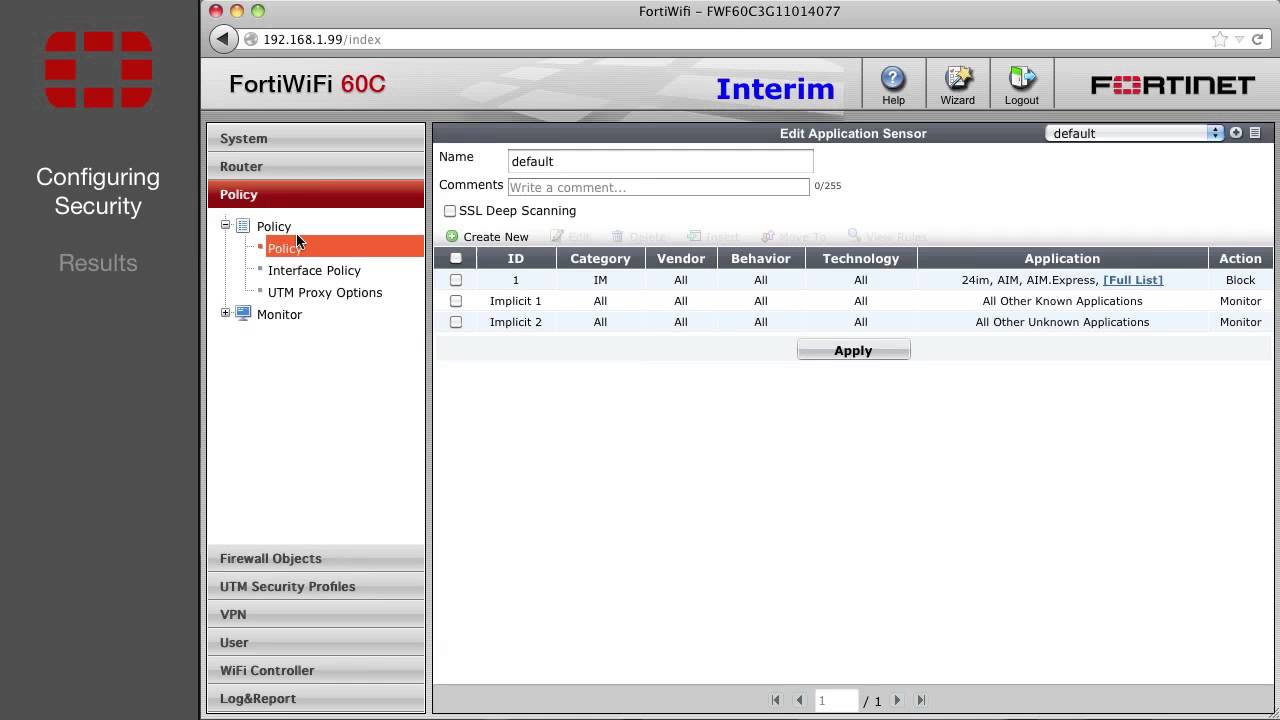
Fortigate Firewall Training - How To block specific CountryDescription This article explains how to block the below over Internet Server Database: top.bitcoinadvocacy.shop (can be used only as. Three new web filter categories have been added to the FortiOS and FortiGuard servers: URL shortening (97), crypto mining (98), and potentially unwanted program. I currently use: top.bitcoinadvocacy.shop Botnet-C&top.bitcoinadvocacy.shop top.bitcoinadvocacy.shop Phishing.